Identify Your Security Gaps in 7–10 Days
A focused assessment to uncover risks, improve security, and give you a clear roadmap — without disrupting your operations.
What You Get



Who This Is For

Fintech companies handling sensitive data
Fintech companies managing sensitive financial transactions and customer data while ensuring strong cybersecurity, regulatory compliance, and continuous protection against evolving cyber threats and fraud risks.

Organisations scaling cloud infrastructure
Organisations expanding secure and scalable cloud infrastructure environments that require reliable security architecture, cloud governance, and protection for critical applications and financial systems
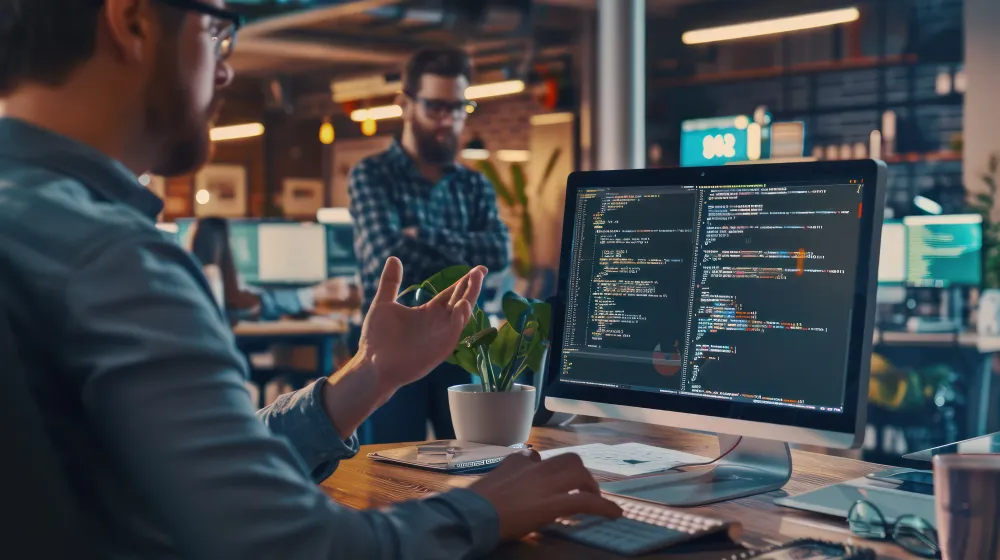
Teams lacking visibility into security risks
Technology teams needing better visibility into evolving cybersecurity risks with centralized monitoring, threat detection, and improved control across cloud platforms, applications, and infrastructure.
How It Works ?
1.Initial Consultation
We begin with a consultation to understand your business environment, security concerns, and infrastructure requirements, ensuring we align the assessment with your organisation’s technology and compliance goals.
2.System and infrastructure review
Our experts perform a detailed review of your existing systems, cloud infrastructure, and security configurations to evaluate vulnerabilities, architecture design, and operational security practices.
3.Risk identification
We analyse potential security gaps, misconfigurations, and threat exposure points that could impact your systems, helping identify risks related to data protection, access control, and network security.
4.Delivery of report + roadmap
You receive a comprehensive security report along with a clear roadmap outlining recommended improvements, security controls, and actionable steps to strengthen your infrastructure and compliance posture.