Secure Your Infrastructure. Meet Compliance. Scale Without Risk.
What We Do
We design and implement:
Aman Cloud delivers secure cloud infrastructure, cybersecurity architecture, DevSecOps pipelines, and identity management solutions. With a security-first approach and expert cloud engineers, we help businesses build scalable, reliable, and future-ready IT environments.
From Zero Trust security frameworks to Microsoft Azure cloud deployments, our solutions are designed to protect critical systems while enabling seamless growth and innovation. We integrate advanced technologies, automation, and best practices to ensure high performance, strong security, and operational efficiency. Our goal is to empower organizations with modern, resilient digital infrastructures that support long-term success.
Who We Work With

Modern financial and fintech companies require secure, scalable infrastructure to protect sensitive data while supporting fast innovation and digital services

Government organisations need reliable, compliant cloud environments that ensure data protection, operational transparency, and secure digital services

Large enterprises require resilient cloud platforms that support complex operations, strong security controls, and scalable infrastructure for growth.
The Problem
Most organisations:
Bolt security on after deployment

Lack visibility across systems

Slow down due to manual security processes
Our Approach
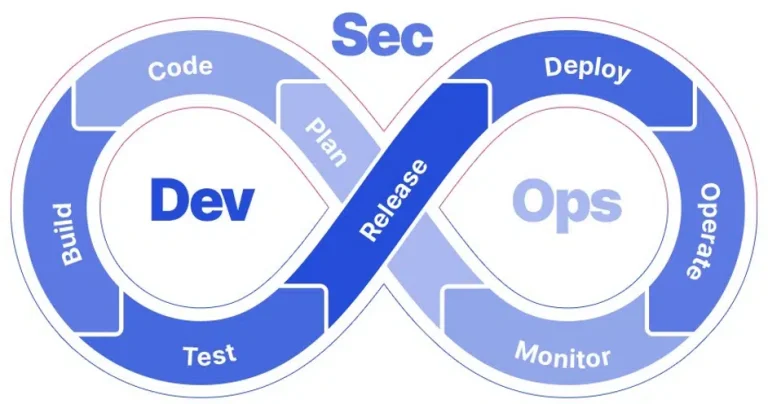
We embed security directly into your infrastructure and development lifecycle:
At Aman Cloud, we believe security should not be an afterthought. Instead of adding protection after systems are built, we integrate security directly into the foundation of your infrastructure and development lifecycle. Our approach focuses on designing secure cloud environments from day one, ensuring that every layer of your architecture is built with protection, scalability, and compliance in mind.
We implement automated security within CI/CD pipelines so that vulnerabilities are detected and addressed early in the development process. Through continuous monitoring, advanced threat detection, and identity-first access control, we help organizations maintain full visibility across their systems while reducing manual security efforts. This proactive, security-first strategy allows businesses to innovate faster while staying compliant and protected