Industries We Serve
We help regulated and high-growth organisations secure, scale, and operate their digital
infrastructure with confidence.

Tailored IT Solutions for Every Sector
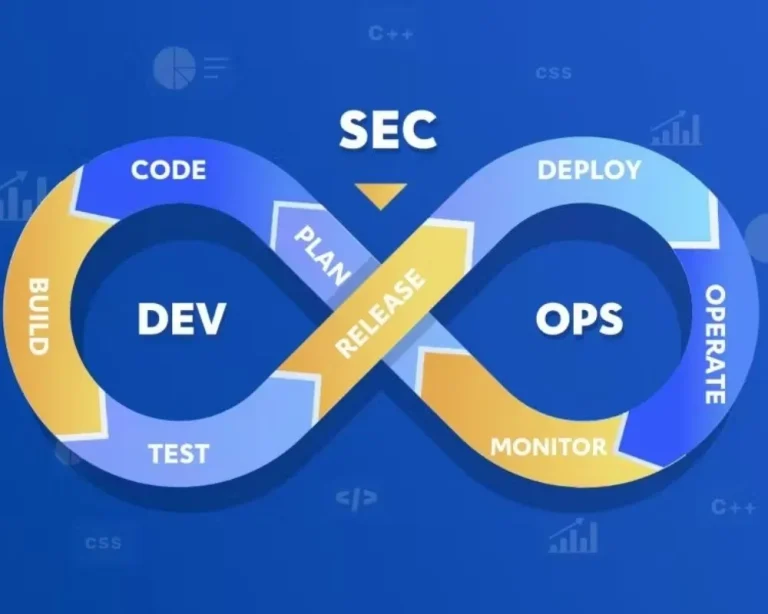
At Aman Cloud, we understand that every industry faces its own set of challenges, regulations, and opportunities. A one-size-fits-all approach doesn’t work in today’s competitive environment—that’s why our cloud, cybersecurity, and DevSecOps solutions are carefully tailored to address the specific demands of each sector.
Whether it’s protecting sensitive financial data, ensuring compliance in healthcare, scaling retail platforms, or enabling faster innovation for startups, our team of experts brings deep domain knowledge and a security-first mindset to every project. We don’t just provide technology—we design industry-focused strategies that align with your business goals and deliver measurable results
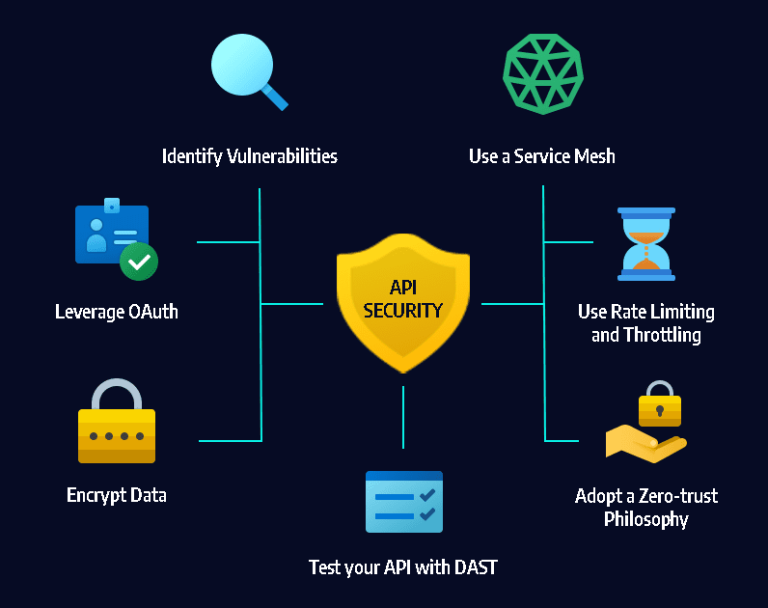
Financial Services & Fintech
The Challenge

Regulatory pressure (PCI-DSS, GDPR, local compliance)
High risk of data breaches and fraud

Rapid product development with security gaps

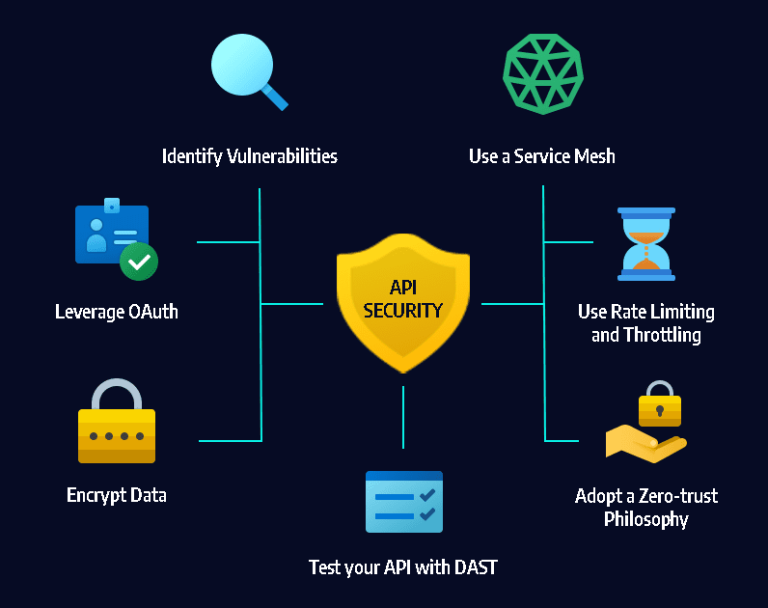
API vulnerabilities and cloud misconfigurations
What We Do
Secure cloud architecture for banking and fintech platforms

DevSecOps pipelines with automated security testing

Identity & access management (Zero Trust, MFA, Conditional Access)

API and application security

Secure cloud architecture for banking and fintech platforms
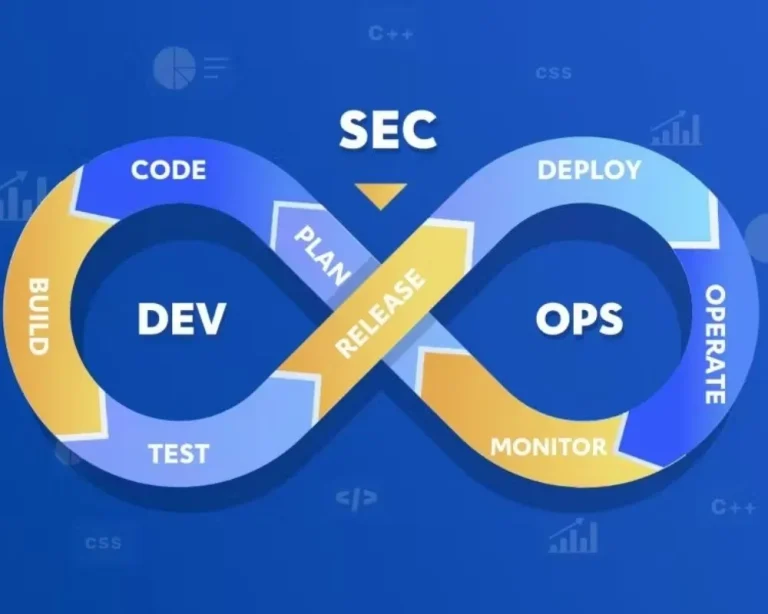
DevSecOps pipelines with automated security testing

Identity & access management (Zero Trust, MFA, Conditional Access)

API and application security
out come

Improved system visibility and control
Secure scaling across teams
Reduced downtime and operational risk
Book a Fintech Security Assessment
Government & Public Sector
The Challenge

Legacy systems with security gaps
Data sovereignty and compliance requirements

Complex infrastructure across departments
High-value cyber attack targets
What We Do

Secure cloud transformation and infrastructure hardening

Identity and access control across departments

Microsoft security stack implementation (Defender, Sentinel)
Compliance-aligned architecture

Secure cloud transformation and infrastructure hardening

Identity and access control across departments
Microsoft security stack implementation (Defender, Sentinel)

Compliance-aligned architecture
out come

Secure, scalable public services
Reduced operational risk

Improved compliance readiness
Speak to a Government Cloud Specialist
Enterprise & Corporate Organisations
The Challenge
Fragmented IT environments
Lack of visibility across systems

Increasing cyber threats

Scaling securely across teams and locations
What We Do

End-to-end cloud infrastructure design and optimisation

Endpoint and identity protection

Secure collaboration environments (Microsoft 365)
DevSecOps integration for internal development teams

End-to-end cloud infrastructure design and optimisation

Endpoint and identity protection
Secure collaboration environments (Microsoft 365)

DevSecOps integration for internal development teams
out come
Improved system visibility and control
Secure scaling across teams

Reduced downtime and operational risk
Request an Infrastructure & Security Review
AI & Digital Platforms
The Challenge

Securing AI models and data pipelines
Unprotected APIs and endpoints

Lack of governance in AI deployment

Rapid scaling without security controls
What We Do

Secure AI deployment pipelines

Data protection and access control

API security and monitoring

Cloud infrastructure for AI workloads
Secure AI deployment pipelines

Data protection and access control

API security and monitoring

Cloud infrastructure for AI workloads
out come
Secure AI deployment at scale
Reduced data and model risk

Controlled and compliant AI environments
Secure Your AI Infrastructure
Healthcare
The Challenge

Protecting sensitive patient and medical data
Strict regulatory and data privacy requirements
Legacy systems and fragmented healthcare infrastructure

Increasing cyber threats targeting healthcare institutions
What We Do

Secure cloud infrastructure for healthcare platforms

Identity and access management for clinical systems

Data protection and encryption for sensitive health records

Compliance-aligned architecture for regulated environments

Secure cloud infrastructure for healthcare platforms

Identity and access management for clinical systems

Data protection and encryption for sensitive health records

Compliance-aligned architecture for regulated environments
out come
Secure and reliable healthcare systems

Protected patient data and improved privacy
Scalable infrastructure for modern healthcare services
Speak to a Healthcare Cloud Specialist
Retail & E-commerce
The Challenge

Protecting customer data and payment transactions

Securing APIs, payment gateways, and digital storefronts

Managing high traffic during peak shopping periods

Preventing fraud and cyber threats targeting online platforms
What We Do
Secure and scalable cloud infrastructure for e-commerce platforms

Payment system and API security implementation

Identity, access management, and data protection controls

Continuous monitoring and threat detection for online platforms

Secure and scalable cloud infrastructure for e-commerce platforms
Payment system and API security implementation

Identity, access management, and data protection controls

Continuous monitoring and threat detection for online platforms
out come

Secure and reliable online shopping experiences

Protected customer data and payment systems
Scalable infrastructure supporting business growth
Speak to a Retail & E-commerce Cloud Specialist
Education
The Challenge

Protecting student data and institutional records

Managing growing digital learning platforms and systems
Securing online portals, applications, and user access

Ensuring reliable infrastructure for remote learning environments
What We Do

Secure cloud infrastructure for educational platforms

Identity and access management for students and staff

Data protection and security controls for digital systems

Compliance-aligned architecture for academic environments

Secure cloud infrastructure for educational platforms

Identity and access management for students and staff

Data protection and security controls for digital systems

Compliance-aligned architecture for academic environments
out come

Secure and reliable digital learning environments
Protected customer data and payment systems

Scalable infrastructure supporting modern education
Speak to an Education Cloud Specialist
Why
Aman Cloud ?
01
Security-first approach (not bolted on later)
02
Deep focus on regulated environments
03
Cloud + DevSecOps + Identity in one stack
04
Practical implementation — not just consultancy